Tability is a cheatcode for goal-driven teams. Set perfect OKRs with AI, stay focused on the work that matters.
What are Security Engineer OKRs?
The Objective and Key Results (OKR) framework is a simple goal-setting methodology that was introduced at Intel by Andy Grove in the 70s. It became popular after John Doerr introduced it to Google in the 90s, and it's now used by teams of all sizes to set and track ambitious goals at scale.
Writing good OKRs can be hard, especially if it's your first time doing it. You'll need to center the focus of your plans around outcomes instead of projects.
We understand that setting OKRs can be challenging, so we have prepared a set of examples tailored for Security Engineer. Take a peek at the templates below to find inspiration and kickstart your goal-setting process.
If you want to learn more about the framework, you can read our OKR guide online.
The best tools for writing perfect Security Engineer OKRs
Here are 2 tools that can help you draft your OKRs in no time.
Tability AI: to generate OKRs based on a prompt
Tability AI allows you to describe your goals in a prompt, and generate a fully editable OKR template in seconds.
- 1. Create a Tability account
- 2. Click on the Generate goals using AI
- 3. Describe your goals in a prompt
- 4. Get your fully editable OKR template
- 5. Publish to start tracking progress and get automated OKR dashboards
Watch the video below to see it in action 👇
Tability Feedback: to improve existing OKRs
You can use Tability's AI feedback to improve your OKRs if you already have existing goals.
- 1. Create your Tability account
- 2. Add your existing OKRs (you can import them from a spreadsheet)
- 3. Click on Generate analysis
- 4. Review the suggestions and decide to accept or dismiss them
- 5. Publish to start tracking progress and get automated OKR dashboards
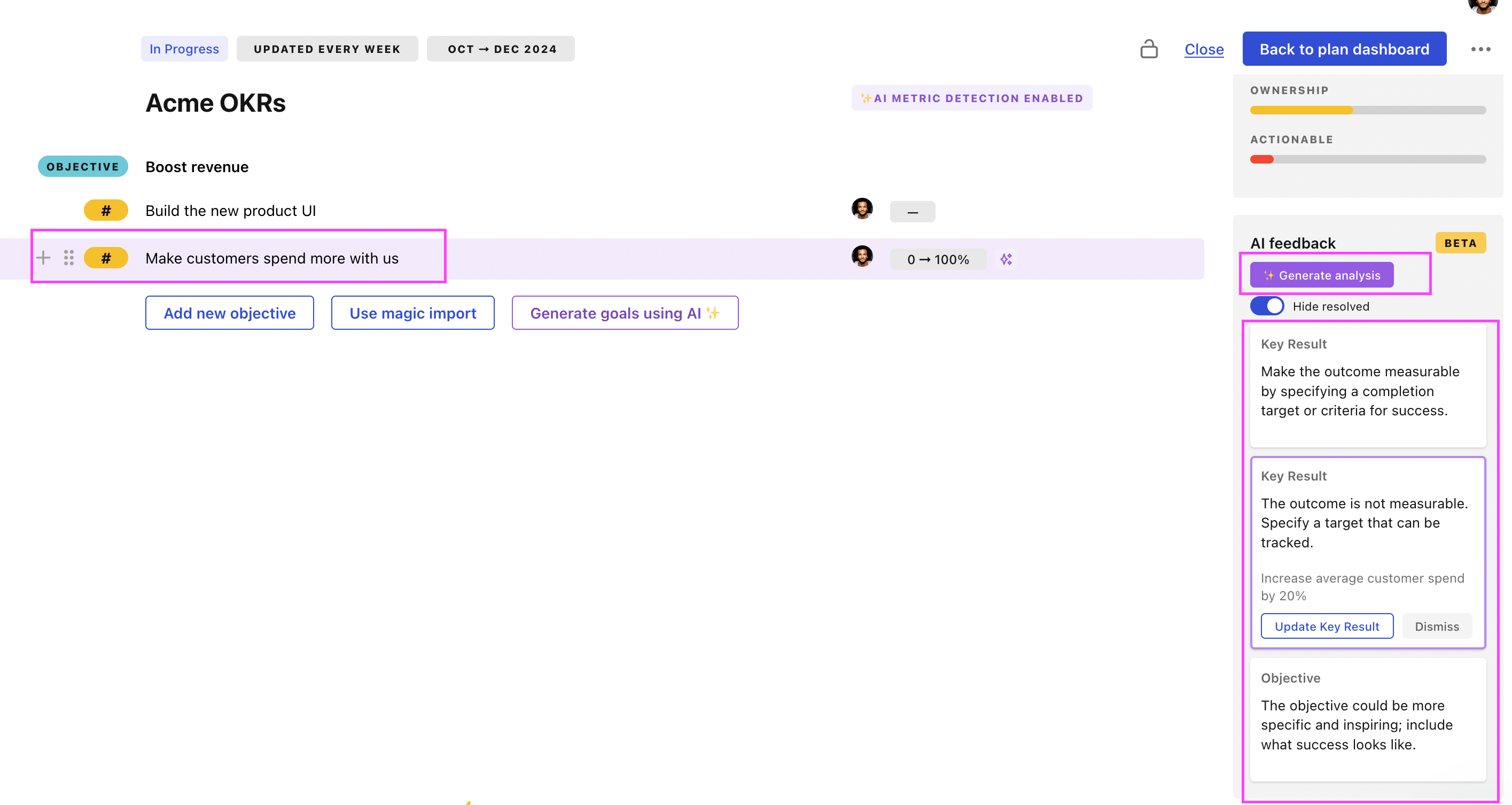
Tability will scan your OKRs and offer different suggestions to improve them. This can range from a small rewrite of a statement to make it clearer to a complete rewrite of the entire OKR.
Security Engineer OKRs examples
We've added many examples of Security Engineer Objectives and Key Results, but we did not stop there. Understanding the difference between OKRs and projects is important, so we also added examples of strategic initiatives that relate to the OKRs.
Hope you'll find this helpful!
OKRs to implement cutting-edge bot detection technologies for website data
ObjectiveImplement cutting-edge bot detection technologies for website data
KRAchieve 95% accuracy rate in detecting bots using newly implemented technologies
Continuously refine and update the models deployed
Test algorithms with diverse sets of data
Implement new machine learning algorithms for bot detection
KRIntegrate and test 3 selected bot detection technologies on our website
Choose three suitable bot detection technologies for our website
Conduct thorough testing to ensure effectiveness
Implement these technologies into our site's backend
KRIdentify and study 10 new bot detection methods from industry research
Analyze each method's pros, cons, and applicability
Select 10 recent industry research on bot detection methods
Prepare a report summarizing findings
OKRs to securely integrate Code42 and Abnormal Security with existing operations
ObjectiveSecurely integrate Code42 and Abnormal Security with existing operations
KRDevelop, test, and validate 3 playbooks for Abnormal Security integration
Write codes for 3 Abnormal Security integration playbooks
Validate the effectiveness and efficiency of each playbook
Test the functionality of all 3 playbooks
KRDefine and document 3 playbooks for Code42 integration without security breaches
Ensure secure procedures are incorporated into guides
Document the integration process explicitly
Identify necessary features for Code42 integration playbooks
KRMeasure and ensure 90% of staff are trained on the new playbooks implementation
Schedule and conduct training sessions with staff members
Conduct surveys or tests to confirm 90% staff training completion
Develop extensive training modules for new playbooks implementation
OKRs to enhance security operation centre's monitoring tools
ObjectiveEnhance security operation centre's monitoring tools
KRIncrease tool detection accuracy by 20%
Enhance image recognition algorithms for improved tool detection
Implement regular system audits and accuracy checks
Arrange continuous team training for precision calibration techniques
KRReduce false positive alerts by 30%
Conduct regular system accuracy checks
Review and refine existing alert parameters
Implement improved machine learning algorithms
KRImplement at least 2 new, relevant monitoring features
Develop and test new monitoring features
Identify potential monitoring features aligned with business needs
Deploy and evaluate the new features
OKRs to successfully migrate all applications to a secure DevOps pipeline
ObjectiveSuccessfully migrate all applications to a secure DevOps pipeline
KRAchieve zero security incidents post-migration in the reviewed applications
Regularly review and update security measures
Implement solid security mechanisms post-migration
Conduct thorough security checks and audits before migration
KRTrain 80% of development team on secure DevOps pipeline management
Identify team members needing secure DevOps pipeline training
Organize a training program with a competent instructor
Schedule and implement training sessions for identified members
KRImplement secure DevOps pipeline framework for 50% of existing applications
Develop or acquire the necessary secure DevOps pipeline framework
Identify applications suitable for secure DevOps pipeline implementation
Roll out the framework across the identified applications
OKRs to conduct regular penetration testing and code reviews
ObjectiveImprove security through regular penetration testing and code reviews
KREnsure all critical vulnerabilities found in penetration testing are remediated within 2 weeks
KRConduct code reviews for all new features and major changes before deployment
KRImplement at least 80% of code review recommendations within the next release cycle
KRIncrease the frequency of penetration testing from once a quarter to twice a month
OKRs to increase efficiency and scalability through cloud deployment
ObjectiveIncrease efficiency and scalability through cloud deployment
KREnhance data security by implementing robust cloud security protocols and achieving compliance certifications
Conduct a comprehensive review of current cloud security protocols and identify weaknesses
Regularly monitor and assess cloud security protocols and update as needed
Develop and implement an updated cloud security framework based on industry best practices
Ensure all necessary compliance certifications are achieved and regularly maintained
KRAchieve a minimum of 99.9% uptime by ensuring seamless integration and high availability in the cloud
KRImprove response time by optimizing cloud infrastructure to achieve 20% faster application performance
Analyze current cloud infrastructure to identify performance bottlenecks hindering application response time
Optimize code and queries by analyzing and improving inefficient code segments
Utilize content delivery network (CDN) for faster content delivery and reduced latency
Implement caching mechanisms to store frequently accessed data and minimize database calls
KRReduce infrastructure costs by migrating 80% of applications and services to the cloud
OKRs to enhance SOC SIEM monitoring tools for efficient detection and response
ObjectiveEnhance SOC SIEM monitoring tools for efficient detection and response
KRDecrease response time by 30% by integrating automation into incident response workflows
Identify routine tasks in incident response workflows
Test and refine the automated systems
Implement automation solutions for identified tasks
KRConduct two test scenarios per month to ensure an upgrade in overall system efficiency
Execute two test scenarios regularly
Analyze and document test results for improvements
Identify potential scenarios for system testing
KRIncrease detection accuracy by 20% employing machine learning algorithms to SOC SIEM tools
Test and fine-tune ML algorithms to increase accuracy
Integrate these models with existing SOC SIEM tools
Develop advanced machine learning models for better anomaly detection
OKRs to develop comprehensive USB chip for government use
ObjectiveDevelop comprehensive USB chip for government use
KRFinalize chip design and specifications by testing 5 different iterations
Evaluate test results and finalize chip design and specifications
Conduct thorough testing on each design iteration
Create 5 different chip design iterations for testing
KRManufacture a batch of 500 fully functioning and quality-assured chips
Arrange raw materials and necessary manufacturing machinery
Design technical specifications and blueprint for the chip
Implement robust quality control inspections post-production
KRAccomplish 100% successful installation in government systems without data breach incidences
Monitor the installation process extensively for any unauthorized access
Conduct regular system audits to identify potential weaknesses post-installation
Implement robust security protocols before installation commences
Security Engineer OKR best practices
Generally speaking, your objectives should be ambitious yet achievable, and your key results should be measurable and time-bound (using the SMART framework can be helpful). It is also recommended to list strategic initiatives under your key results, as it'll help you avoid the common mistake of listing projects in your KRs.
Here are a couple of best practices extracted from our OKR implementation guide 👇
Tip #1: Limit the number of key results
The #1 role of OKRs is to help you and your team focus on what really matters. Business-as-usual activities will still be happening, but you do not need to track your entire roadmap in the OKRs.
We recommend having 3-4 objectives, and 3-4 key results per objective. A platform like Tability can run audits on your data to help you identify the plans that have too many goals.
Tip #2: Commit to weekly OKR check-ins
Don't fall into the set-and-forget trap. It is important to adopt a weekly check-in process to get the full value of your OKRs and make your strategy agile – otherwise this is nothing more than a reporting exercise.
Being able to see trends for your key results will also keep yourself honest.
Tip #3: No more than 2 yellow statuses in a row
Yes, this is another tip for goal-tracking instead of goal-setting (but you'll get plenty of OKR examples above). But, once you have your goals defined, it will be your ability to keep the right sense of urgency that will make the difference.
As a rule of thumb, it's best to avoid having more than 2 yellow/at risk statuses in a row.
Make a call on the 3rd update. You should be either back on track, or off track. This sounds harsh but it's the best way to signal risks early enough to fix things.
Save hours with automated OKR dashboards
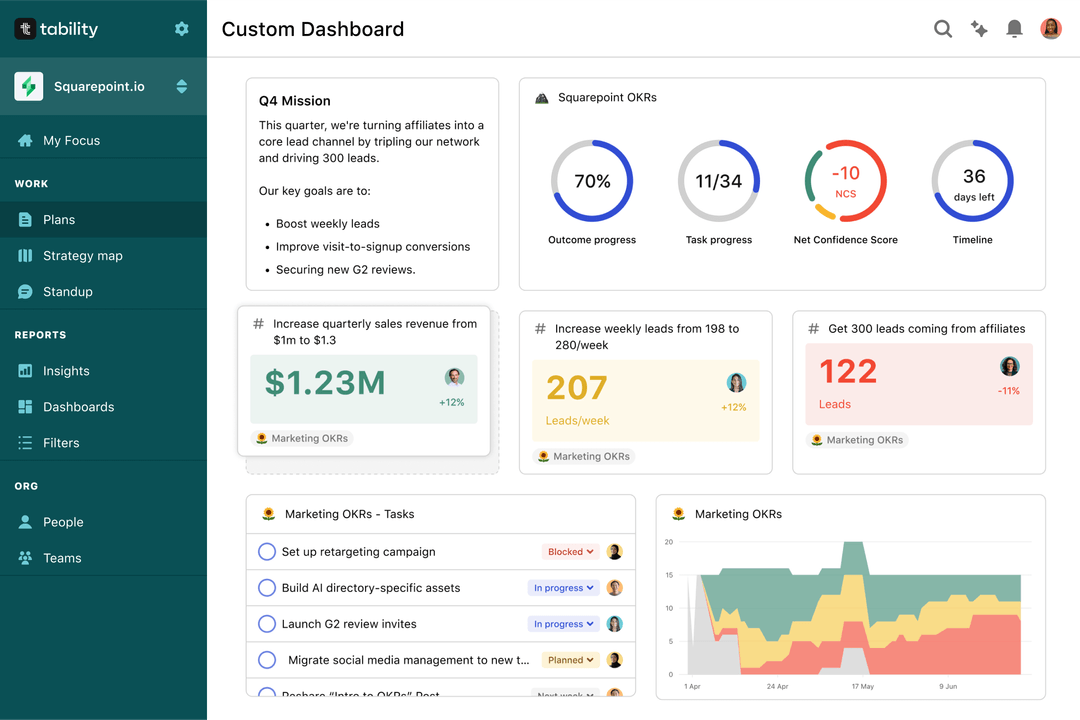
The rules of OKRs are simple. Quarterly OKRs should be tracked weekly, and yearly OKRs should be tracked monthly. Reviewing progress periodically has several advantages:
- It brings the goals back to the top of the mind
- It will highlight poorly set OKRs
- It will surface execution risks
- It improves transparency and accountability
Spreadsheets are enough to get started. Then, once you need to scale you can use Tability to save time with automated OKR dashboards, data connectors, and actionable insights.
How to get Tability dashboards:
- 1. Create a Tability account
- 2. Use the importers to add your OKRs (works with any spreadsheet or doc)
- 3. Publish your OKR plan
That's it! Tability will instantly get access to 10+ dashboards to monitor progress, visualise trends, and identify risks early.
More Security Engineer OKR templates
We have more templates to help you draft your team goals and OKRs.
OKRs to ensure provision of top-tier, cost-efficient education
OKRs to amplify data analysis abilities
OKRs to implement an AI tool for efficient user manual generation
OKRs to graduate on schedule without extra classes
OKRs to enhance Team Collaboration
OKRs to elevate overall customer satisfaction and loyalty