OKR template to enhance proactive investigation through expanded log analysis
Your OKR template
Furthermore, the OKR seeks to improve threat identification by 40% via team training on a new tool. This will involve conducting a comprehensive training session, measuring improvements post-training, and selecting team members for threat identification training.
Implementing an advanced log analysis tool for automated identification and flagging of potential threats also forms part of this OKR. Achieving this will involve researching and selecting a suitable tool, training the IT team on threat identification and response, and installing and configuring the selected tool.
Overall, the OKR's emphasis lies in improving threat identification, swift response and automated analysis of logs for better security management. Detailed planning and training are essential for its successful implementation.
ObjectiveEnhance proactive investigation through expanded log analysis
KRLower the average response time to identified threats by 20%
Seek professional consultation on response strategy
Implement advanced threat detection software
Train staff to swiftly respond to threats
KRTrain the team on the new tool to improve threat identification by 40%
Organize a comprehensive training session on the new tool
Measure improvements in threat identification post-training
Select team members to participate in threat identification training
KRImplement advance log analysis tool to automatically identify and flag potential threats
Research and select an advanced log analysis tool
Train IT team on threat identification and response
Install and configure the chosen tool
How to edit and track OKRs with Tability
You'll probably want to edit the examples in this post, and Tability is the perfect tool for it.
Tability is an AI-powered platform that helps teams set better goals, monitor execution, and get help to achieve their objectives faster.
With Tability you can:
- Use AI to draft a complete set of OKRs in seconds
- Connect your OKRs and team goals to your project
- Automate reporting with integrations and built-in dashboard
Instead of having to copy the content of the OKR examples in a doc or spreadsheet, you can use Tability’s magic importer to start using any of the examples in this page.
The import process can be done in seconds, allowing you to edit OKRs directly in a platform that knows how to manage and track goals.
Step 1. Sign up for a free Tability account
Go tohttps://tability.app/signup and create your account (it's free!)
Step 2. Create a plan
Follow the steps after your onboarding to create your first plan, you should get to a page that looks like the picture below.
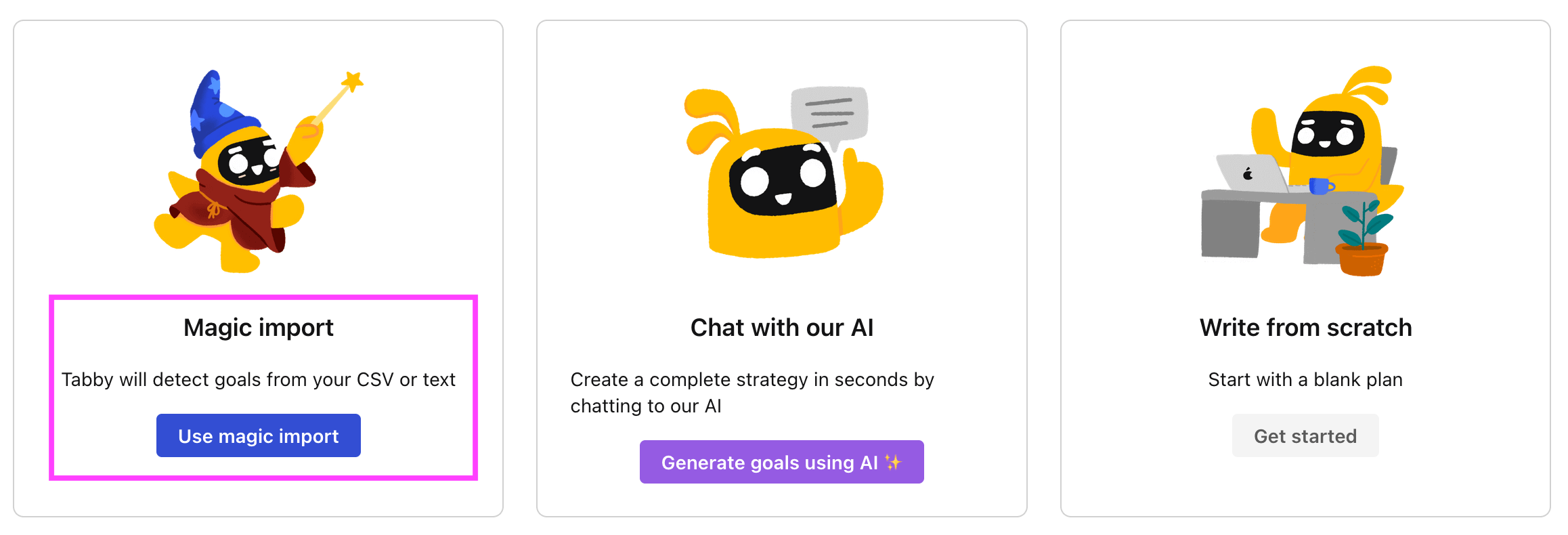
Step 3. Use the magic importer
Click on Use magic import to open up the Magic Import modal.
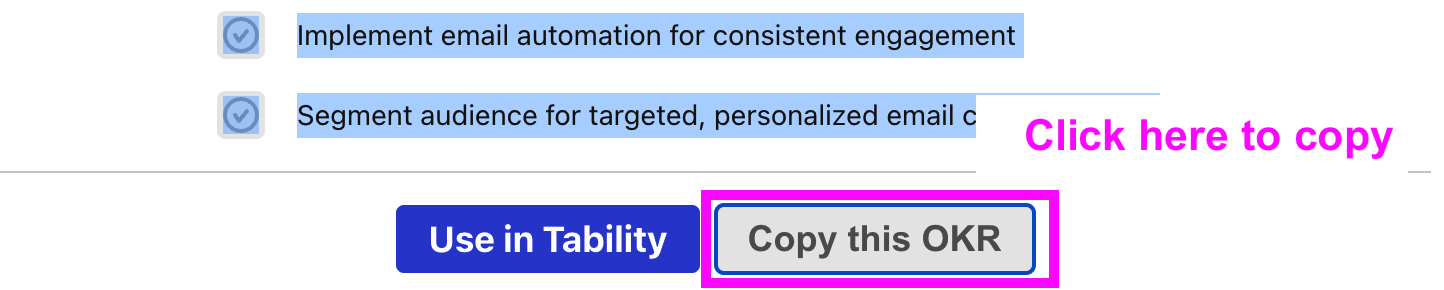
Now, go back to the OKR examples, and click on Copy on the example that you’d like to use.
Paste the content in the text import section. Don’t worry about the formatting, Tability’s AI will be able to parse it!
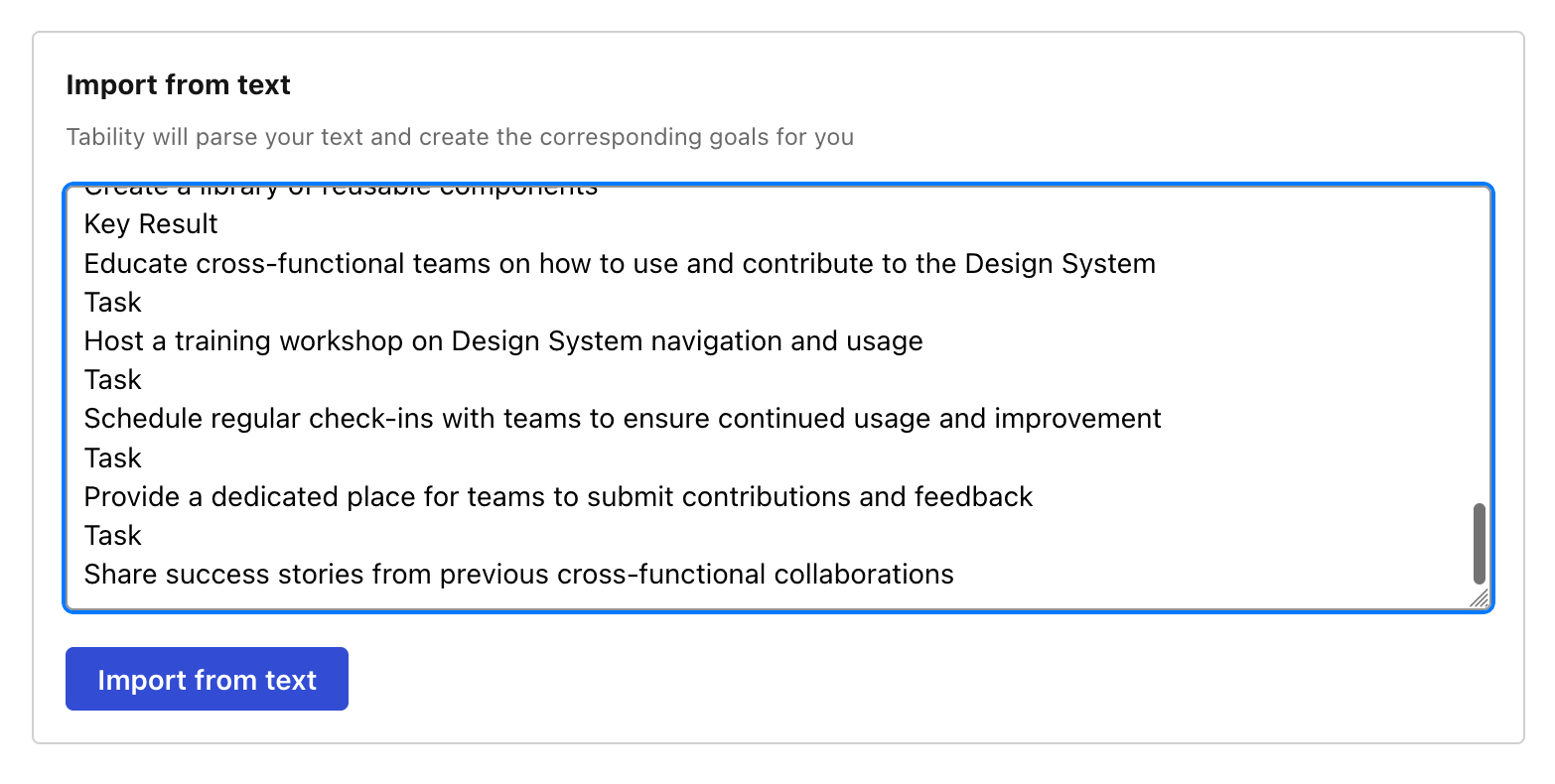
Now, just click on Import from text and let the magic happen.
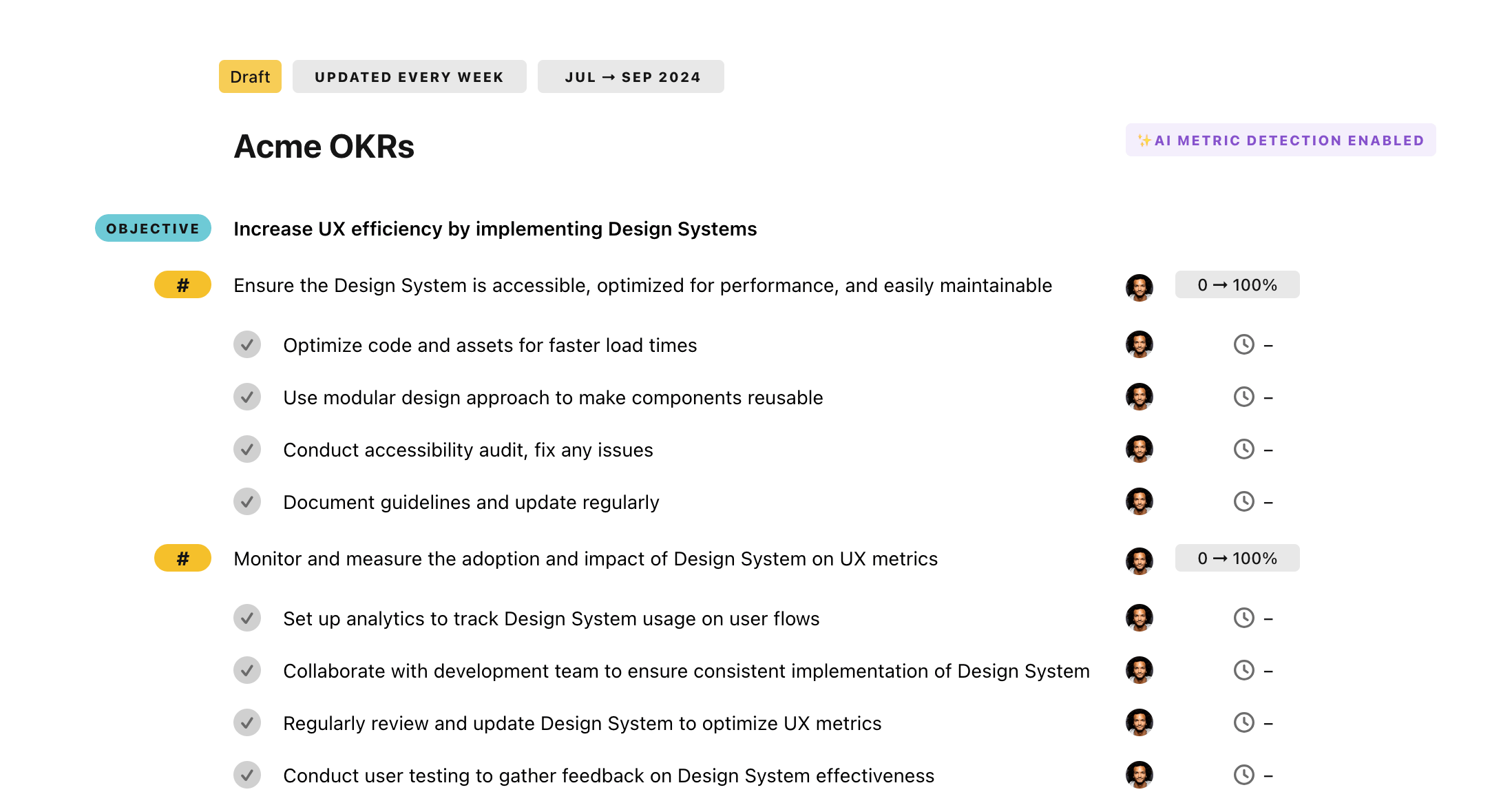
Once your example is in the plan editor, you will be able to:
- Edit the objectives, key results, and tasks
- Click on the target 0 → 100% to set better target
- Use the tips and the AI to refine your goals
Step 4. Publish your plan
Once you’re done editing, you can publish your plan to switch to the goal-tracking mode.
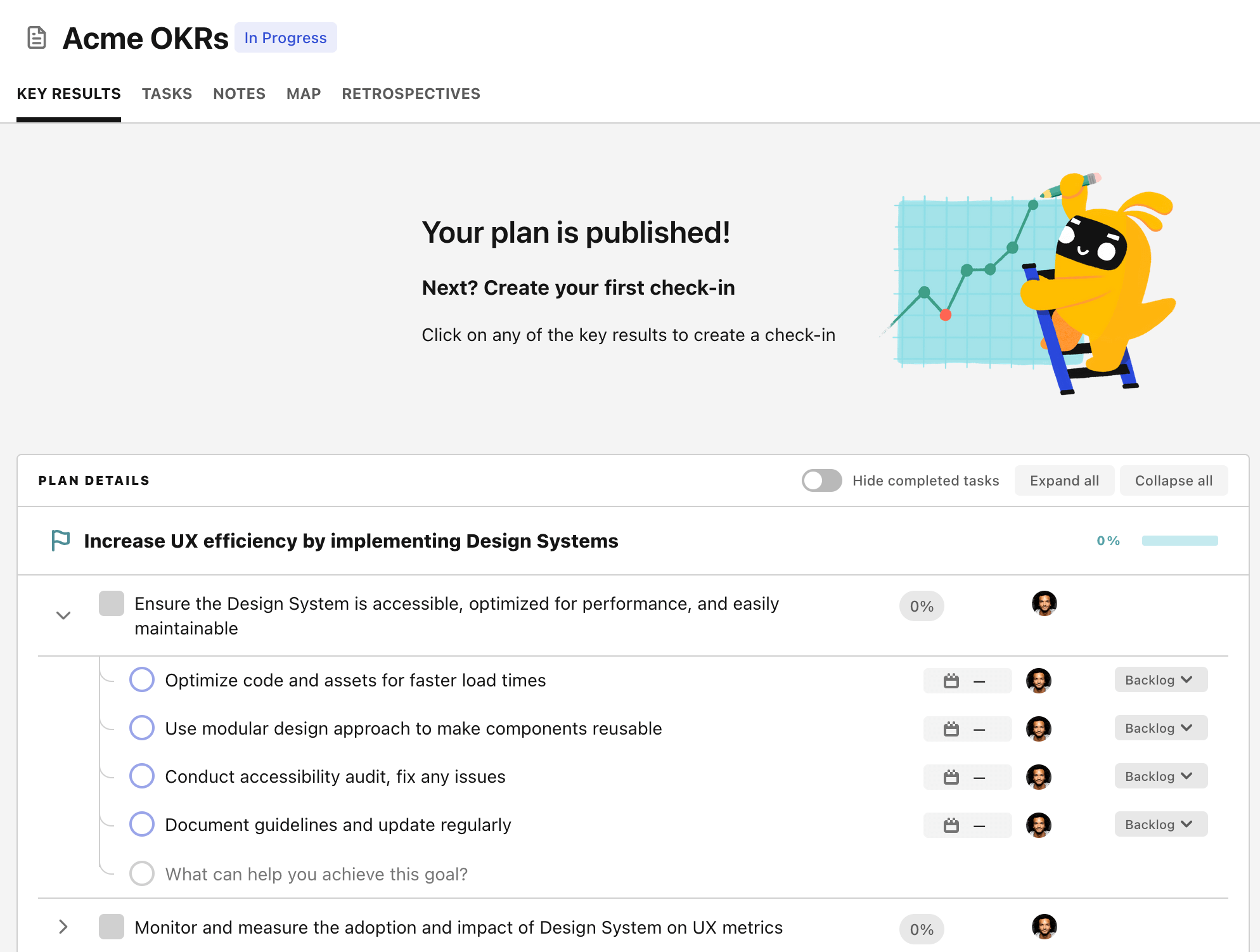
From there you will have access to all the features that will help you and your team save hours with OKR reporting.
- 10+ built-in dashboards to visualise progress on your goals
- Weekly reminders, data connectors, and smart notifications
- 9 views to map OKRs to strategic projects
- Strategy map to align teams at scale