Tability is a cheatcode for goal-driven teams. Set perfect OKRs with AI, stay focused on the work that matters.
What are Security Expert OKRs?
The Objective and Key Results (OKR) framework is a simple goal-setting methodology that was introduced at Intel by Andy Grove in the 70s. It became popular after John Doerr introduced it to Google in the 90s, and it's now used by teams of all sizes to set and track ambitious goals at scale.
Writing good OKRs can be hard, especially if it's your first time doing it. You'll need to center the focus of your plans around outcomes instead of projects.
We understand that setting OKRs can be challenging, so we have prepared a set of examples tailored for Security Expert. Take a peek at the templates below to find inspiration and kickstart your goal-setting process.
If you want to learn more about the framework, you can read our OKR guide online.
The best tools for writing perfect Security Expert OKRs
Here are 2 tools that can help you draft your OKRs in no time.
Tability AI: to generate OKRs based on a prompt
Tability AI allows you to describe your goals in a prompt, and generate a fully editable OKR template in seconds.
- 1. Create a Tability account
- 2. Click on the Generate goals using AI
- 3. Describe your goals in a prompt
- 4. Get your fully editable OKR template
- 5. Publish to start tracking progress and get automated OKR dashboards
Watch the video below to see it in action 👇
Tability Feedback: to improve existing OKRs
You can use Tability's AI feedback to improve your OKRs if you already have existing goals.
- 1. Create your Tability account
- 2. Add your existing OKRs (you can import them from a spreadsheet)
- 3. Click on Generate analysis
- 4. Review the suggestions and decide to accept or dismiss them
- 5. Publish to start tracking progress and get automated OKR dashboards
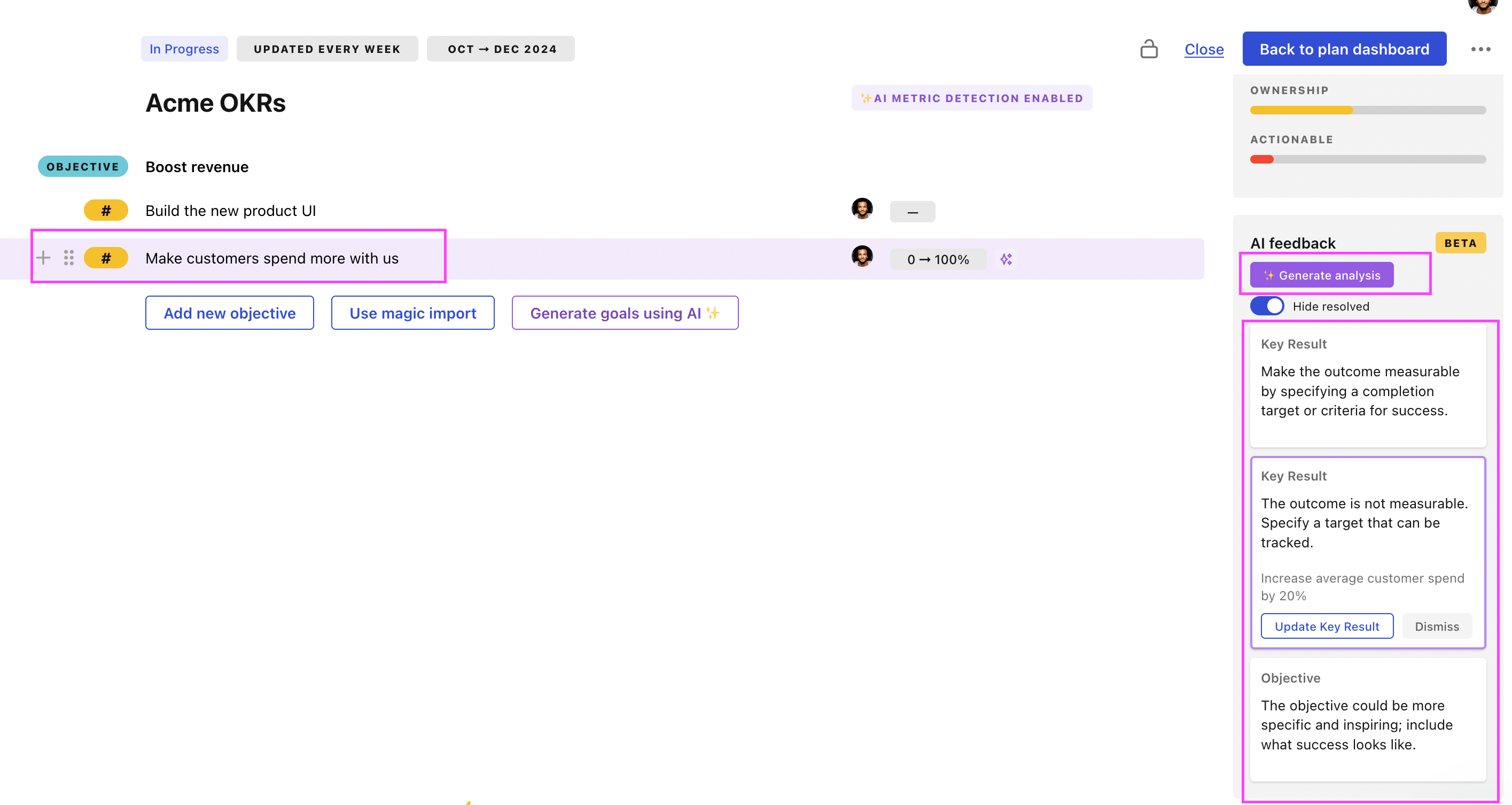
Tability will scan your OKRs and offer different suggestions to improve them. This can range from a small rewrite of a statement to make it clearer to a complete rewrite of the entire OKR.
Security Expert OKRs examples
You'll find below a list of Objectives and Key Results templates for Security Expert. We also included strategic projects for each template to make it easier to understand the difference between key results and projects.
Hope you'll find this helpful!
OKRs to enhance system security for robust protection
ObjectiveEnhance system security for robust protection
KRAchieve a 95% score in independent security audits validating system security protocols
Implement necessary updates and enhancements to address identified security gaps
Collaborate with external security experts to perform comprehensive security audits
Conduct thorough review of current security protocols and identify areas for improvement
Continuously monitor and evaluate system security measures to maintain a 95% audit score
KRReduce number of security breaches by 20% through enhanced authentication measures
Train employees on best practices for recognizing and avoiding phishing attacks
Implement two-factor authentication system for all users
Enhance password requirements and enforce regular password updates
Conduct regular security audits to identify vulnerabilities and address them promptly
KRImprove application vulnerability by reducing critical security issues by 15%
Train developers and staff on secure coding practices and security best practices
Implement regular security audits and vulnerability assessments on the application
Update and patch software and libraries regularly to address security vulnerabilities
Implement stricter access controls and enforce strong password policies for application access
KRIncrease employee awareness through mandatory security training with 100% completion rate
Enforce strict deadlines and reminders to ensure all employees complete the security training
Create an engaging and interactive security training program for all employees
Evaluate the effectiveness of the security training program by conducting regular assessments
Implement a digital platform for employees to easily access and complete security training
OKRs to become a computer security expert
ObjectiveBecome a computer security expert
KRSuccessfully pass the Certified Ethical Hacker (CEH) exam with a score of 80% or higher
KRDevelop and execute a comprehensive security project, receiving positive feedback from industry experts
Collaborate with industry experts to gather insights and recommendations for improving security measures
Regularly monitor and evaluate the effectiveness of implemented security measures to ensure ongoing protection
Develop and implement robust security protocols and controls across all systems and processes
Conduct a thorough assessment of current security vulnerabilities and risks
KRComplete at least two online courses on computer security, scoring above 90% in each
Ensure mastery of course materials and aim to score above 90% in assessments
Devote dedicated hours per week to studying and completing the online courses
Research and identify two reputable online courses for computer security
Enroll in the selected online courses on computer security
KRImplement and manage effective security measures on personal computer resulting in zero malware incidents
Install a reliable antivirus software program on the personal computer
Enable automatic software updates for the operating system and all installed applications
Avoid clicking on suspicious links or downloading files from untrustworthy sources
Regularly update the antivirus software to ensure the latest protection against malware
OKRs to enhance AWS resilience against DDoS through PenTest, gap assessment and remediation
ObjectiveEnhance AWS resilience against DDoS through PenTest, gap assessment and remediation
KRComplete gap assessment, identifying 100% of the areas vulnerable to DDoS attacks
Implement preventative measures to address all identified vulnerabilities
Identify all components of your organization's network infrastructure
Hire a cybersecurity expert to perform a gap assessment
KRDevelop and implement a remediation strategy, reducing DDoS vulnerabilities by 50%
Identify current DDoS vulnerabilities in the system
Develop a comprehensive remediation strategy
Implement the remediation strategy across the system
KRConduct comprehensive PenTesting on all AWS components to identify potential vulnerabilities
Compile and assess detailed reports from PenTesting results
Address identified vulnerabilities promptly and efficiently
Engage a professional PenTesting agency to analyze AWS components
Security Expert OKR best practices
Generally speaking, your objectives should be ambitious yet achievable, and your key results should be measurable and time-bound (using the SMART framework can be helpful). It is also recommended to list strategic initiatives under your key results, as it'll help you avoid the common mistake of listing projects in your KRs.
Here are a couple of best practices extracted from our OKR implementation guide 👇
Tip #1: Limit the number of key results
The #1 role of OKRs is to help you and your team focus on what really matters. Business-as-usual activities will still be happening, but you do not need to track your entire roadmap in the OKRs.
We recommend having 3-4 objectives, and 3-4 key results per objective. A platform like Tability can run audits on your data to help you identify the plans that have too many goals.
Tip #2: Commit to weekly OKR check-ins
Don't fall into the set-and-forget trap. It is important to adopt a weekly check-in process to get the full value of your OKRs and make your strategy agile – otherwise this is nothing more than a reporting exercise.
Being able to see trends for your key results will also keep yourself honest.
Tip #3: No more than 2 yellow statuses in a row
Yes, this is another tip for goal-tracking instead of goal-setting (but you'll get plenty of OKR examples above). But, once you have your goals defined, it will be your ability to keep the right sense of urgency that will make the difference.
As a rule of thumb, it's best to avoid having more than 2 yellow/at risk statuses in a row.
Make a call on the 3rd update. You should be either back on track, or off track. This sounds harsh but it's the best way to signal risks early enough to fix things.
Save hours with automated Security Expert OKR dashboards
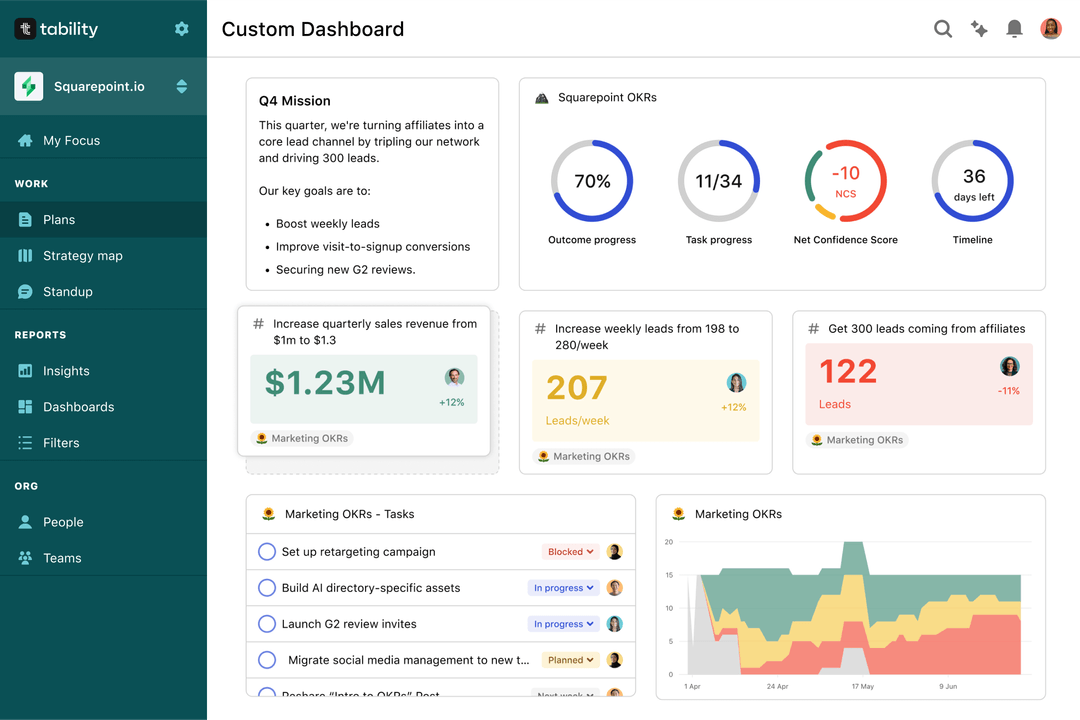
Quarterly OKRs should have weekly updates to get all the benefits from the framework. Reviewing progress periodically has several advantages:
- It brings the goals back to the top of the mind
- It will highlight poorly set OKRs
- It will surface execution risks
- It improves transparency and accountability
Spreadsheets are enough to get started. Then, once you need to scale you can use Tability to save time with automated OKR dashboards, data connectors, and actionable insights.
How to get Tability dashboards:
- 1. Create a Tability account
- 2. Use the importers to add your OKRs (works with any spreadsheet or doc)
- 3. Publish your OKR plan
That's it! Tability will instantly get access to 10+ dashboards to monitor progress, visualise trends, and identify risks early.
More Security Expert OKR templates
We have more templates to help you draft your team goals and OKRs.
OKRs to enhance brand reputation to drive B2B lead generation
OKRs to amplify brand visibility of our SaaS technology through an Account-Based Marketing strategy
OKRs to enhance provision of advisory services
OKRs to deepen understanding of audience content preferences
OKRs to double weekly cocoa purchases from December harvest
OKRs to enhance operational productivity through constant improvement methodology