Tability is a cheatcode for goal-driven teams. Set perfect OKRs with AI, stay focused on the work that matters.
What are System Security OKRs?
The Objective and Key Results (OKR) framework is a simple goal-setting methodology that was introduced at Intel by Andy Grove in the 70s. It became popular after John Doerr introduced it to Google in the 90s, and it's now used by teams of all sizes to set and track ambitious goals at scale.
How you write your OKRs can make a huge difference on the impact that your team will have at the end of the quarter. But, it's not always easy to write a quarterly plan that focuses on outcomes instead of projects.
That's why we have created a list of OKRs examples for System Security to help. You can use any of the templates below as a starting point to write your own goals.
If you want to learn more about the framework, you can read our OKR guide online.
The best tools for writing perfect System Security OKRs
Here are 2 tools that can help you draft your OKRs in no time.
Tability AI: to generate OKRs based on a prompt
Tability AI allows you to describe your goals in a prompt, and generate a fully editable OKR template in seconds.
- 1. Create a Tability account
- 2. Click on the Generate goals using AI
- 3. Describe your goals in a prompt
- 4. Get your fully editable OKR template
- 5. Publish to start tracking progress and get automated OKR dashboards
Watch the video below to see it in action 👇
Tability Feedback: to improve existing OKRs
You can use Tability's AI feedback to improve your OKRs if you already have existing goals.
- 1. Create your Tability account
- 2. Add your existing OKRs (you can import them from a spreadsheet)
- 3. Click on Generate analysis
- 4. Review the suggestions and decide to accept or dismiss them
- 5. Publish to start tracking progress and get automated OKR dashboards
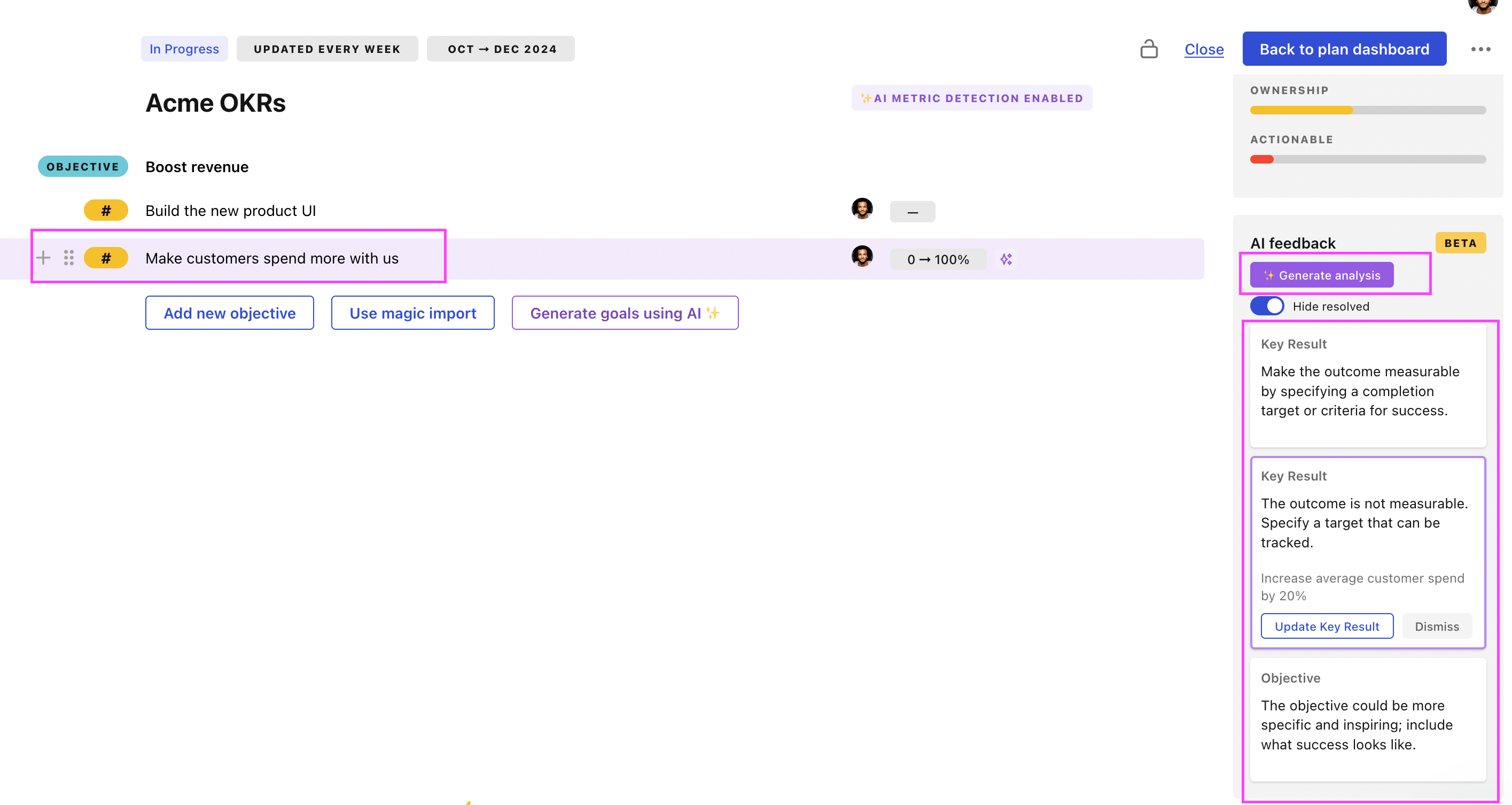
Tability will scan your OKRs and offer different suggestions to improve them. This can range from a small rewrite of a statement to make it clearer to a complete rewrite of the entire OKR.
System Security OKRs examples
We've added many examples of System Security Objectives and Key Results, but we did not stop there. Understanding the difference between OKRs and projects is important, so we also added examples of strategic initiatives that relate to the OKRs.
Hope you'll find this helpful!
OKRs to enhance capabilities for physical security systems management
ObjectiveEnhance capabilities for physical security systems management
KRImplement the integration of 2 new features in existing security systems
Train staff on feature usage and troubleshooting
Test and validate integration of new features
Evaluate current security systems for compatibility with new features
KRIncrease system efficiency by 15% through system upgrades and optimization
Identify areas of the system that require optimization
Purchase and install necessary system upgrades
Regularly monitor and adjust for optimal efficiency
KRDecrease system false-positive alerts by 20%
Refine the current system detection algorithm
Conduct regular system false-positive tests
Implement a more effective filtering system
OKRs to implement integrated technological solutions for physical security systems
ObjectiveImplement integrated technological solutions for physical security systems
KRIdentify and evaluate three top-tier tech-based physical security systems by end of month one
Analyze efficacy and functionalities of selected systems
Research top-tier tech-based physical security systems
Prepare comprehensive evaluation report on each system
KRSuccessfully install and test integration of selected system in a live environment
Install and configure the selected system in a live environment
Conduct thorough testing to ensure successful integration and functionality
Choose appropriate system for integration based on business requirements
KRAchieve 99% functional reliability of the integrated system throughout period and improve by 5%
Introduce software updates to rectify identified bugs
Implement regular maintenance and quality checks for the system
Conduct rigorous system performance evaluations frequently
OKRs to enhance system security for robust protection
ObjectiveEnhance system security for robust protection
KRAchieve a 95% score in independent security audits validating system security protocols
Implement necessary updates and enhancements to address identified security gaps
Collaborate with external security experts to perform comprehensive security audits
Conduct thorough review of current security protocols and identify areas for improvement
Continuously monitor and evaluate system security measures to maintain a 95% audit score
KRReduce number of security breaches by 20% through enhanced authentication measures
Train employees on best practices for recognizing and avoiding phishing attacks
Implement two-factor authentication system for all users
Enhance password requirements and enforce regular password updates
Conduct regular security audits to identify vulnerabilities and address them promptly
KRImprove application vulnerability by reducing critical security issues by 15%
Train developers and staff on secure coding practices and security best practices
Implement regular security audits and vulnerability assessments on the application
Update and patch software and libraries regularly to address security vulnerabilities
Implement stricter access controls and enforce strong password policies for application access
KRIncrease employee awareness through mandatory security training with 100% completion rate
Enforce strict deadlines and reminders to ensure all employees complete the security training
Create an engaging and interactive security training program for all employees
Evaluate the effectiveness of the security training program by conducting regular assessments
Implement a digital platform for employees to easily access and complete security training
OKRs to maintain up-to-date security patches on our infrastructure
ObjectiveMaintain up-to-date security patches on our infrastructure
KRAssess and catalog current state of security patches within two weeks
Create a comprehensive catalog of findings
Identify all systems and software requiring security updates
Verify and document the existing security patches
KRImplement 100% of identified necessary security updates by quarter's end
Develop and execute a schedule for updates
Complete and verify each security update
Identify all required security updates
KRDevelop and initiate routine weekly checks to confirm security patch updates
Establish routine checks for these updates
Identify necessary security patches weekly
Implement and confirm successful patch updates
OKRs to develop comprehensive USB chip for government use
ObjectiveDevelop comprehensive USB chip for government use
KRFinalize chip design and specifications by testing 5 different iterations
Evaluate test results and finalize chip design and specifications
Conduct thorough testing on each design iteration
Create 5 different chip design iterations for testing
KRManufacture a batch of 500 fully functioning and quality-assured chips
Arrange raw materials and necessary manufacturing machinery
Design technical specifications and blueprint for the chip
Implement robust quality control inspections post-production
KRAccomplish 100% successful installation in government systems without data breach incidences
Monitor the installation process extensively for any unauthorized access
Conduct regular system audits to identify potential weaknesses post-installation
Implement robust security protocols before installation commences
OKRs to boost SOC efficiency via AI enhancements and automation implementation
ObjectiveBoost SOC efficiency via AI enhancements and automation implementation
KRTrain all SOC personnel on new AI and automation systems to increase proficiency by 50%
Develop comprehensive training modules on new AI systems
Implement training sessions and measure proficiency increase
Identify AI and automation training needs of all SOC personnel
KRDevelop and integrate at least 2 AI-powered threat detection mechanisms into the SOC
Identify two suitable AI-powered threat detection systems
Implement and test integration of AI systems in SOC
Design integration strategy for the chosen AI systems
KRDecrease response time to identified threats by 30% through automated protocols
Optimize network infrastructure for speedy threat resolution
Implement AI-based threat detection tools for real-time alerting
Train staff on new automated threat response protocols
OKRs to establish unparalleled data leak protection solution
ObjectiveEstablish unparalleled data leak protection solution
KRIncrease client satisfaction regarding data security by 25% through feedback surveys
Analyze survey responses for areas of improvement
Develop and execute strategies to address identified issues
Implement consistent client feedback surveys on data security
KRDevelop and implement a cutting-edge encryption system by increasing R&D team by 15%
Execute full implementation of new encryption system
Identify talent to expand R&D team by an additional 15%
Develop advanced encryption system prototype
KRReduce successful cyber attacks on our system by 80%
Implement multi-factor authentication for all system users
Regularly update and patch system software
Conduct frequent cybersecurity training for employees
OKRs to implement effective vulnerability management processes
ObjectiveStrengthen our vulnerability management procedures
KRReduce high-priority vulnerabilities by 30% through consistent scanning and patching
KRTrain all employees on vulnerability management best practices and create an awareness program
KRImplement a continuous vulnerability scanning process for all systems and applications
KRDevelop and implement a comprehensive vulnerability management policy based on industry standards
OKRs to enhance organizational cybersecurity compliance
ObjectiveEnhance organizational cybersecurity compliance
KRGet certification in ISO 27001 standard for information security management
Develop and implement an information security management system
Research and understand the requirements of ISO 27001 certification
Apply for ISO 27001 certification and prepare for audit
KRAchieve 90% reduction in cybersecurity incidents by bolstering intrusion detection systems
Engage staff in regular cybersecurity training sessions
Enhance existing security measures across all digital touchpoints
Implement advanced intrusion detection system software
KRImplement cybersecurity training for 100% of employees by quarter-end
Track employee attendance and progress
Develop comprehensive cybersecurity training curriculum
Schedule mandatory training sessions for all employees
OKRs to enhance the organization's cybersecurity infrastructure
ObjectiveEnhance the organization's cybersecurity infrastructure
KRImplement multi-factor authentication for all internal systems by the end of Q2
Implement selected multi-factor authentication solution
Assess current authentication methods across all systems
Identify suitable multi-factor authentication solutions
KRConduct cybersecurity training programs for 90% of employees
Identify the key cybersecurity principles for training content
Organize training schedules for employees
Evaluate post-training comprehension and application
KRCarry out system vulnerability assessment every week to spot and fix any gaps
Implement necessary fixes to detected vulnerabilities immediately
Analyze assessment results to identify security gaps
Schedule weekly system vulnerability assessments
System Security OKR best practices
Generally speaking, your objectives should be ambitious yet achievable, and your key results should be measurable and time-bound (using the SMART framework can be helpful). It is also recommended to list strategic initiatives under your key results, as it'll help you avoid the common mistake of listing projects in your KRs.
Here are a couple of best practices extracted from our OKR implementation guide 👇
Tip #1: Limit the number of key results
The #1 role of OKRs is to help you and your team focus on what really matters. Business-as-usual activities will still be happening, but you do not need to track your entire roadmap in the OKRs.
We recommend having 3-4 objectives, and 3-4 key results per objective. A platform like Tability can run audits on your data to help you identify the plans that have too many goals.
Tip #2: Commit to weekly OKR check-ins
Don't fall into the set-and-forget trap. It is important to adopt a weekly check-in process to get the full value of your OKRs and make your strategy agile – otherwise this is nothing more than a reporting exercise.
Being able to see trends for your key results will also keep yourself honest.
Tip #3: No more than 2 yellow statuses in a row
Yes, this is another tip for goal-tracking instead of goal-setting (but you'll get plenty of OKR examples above). But, once you have your goals defined, it will be your ability to keep the right sense of urgency that will make the difference.
As a rule of thumb, it's best to avoid having more than 2 yellow/at risk statuses in a row.
Make a call on the 3rd update. You should be either back on track, or off track. This sounds harsh but it's the best way to signal risks early enough to fix things.
Save hours with automated System Security OKR dashboards
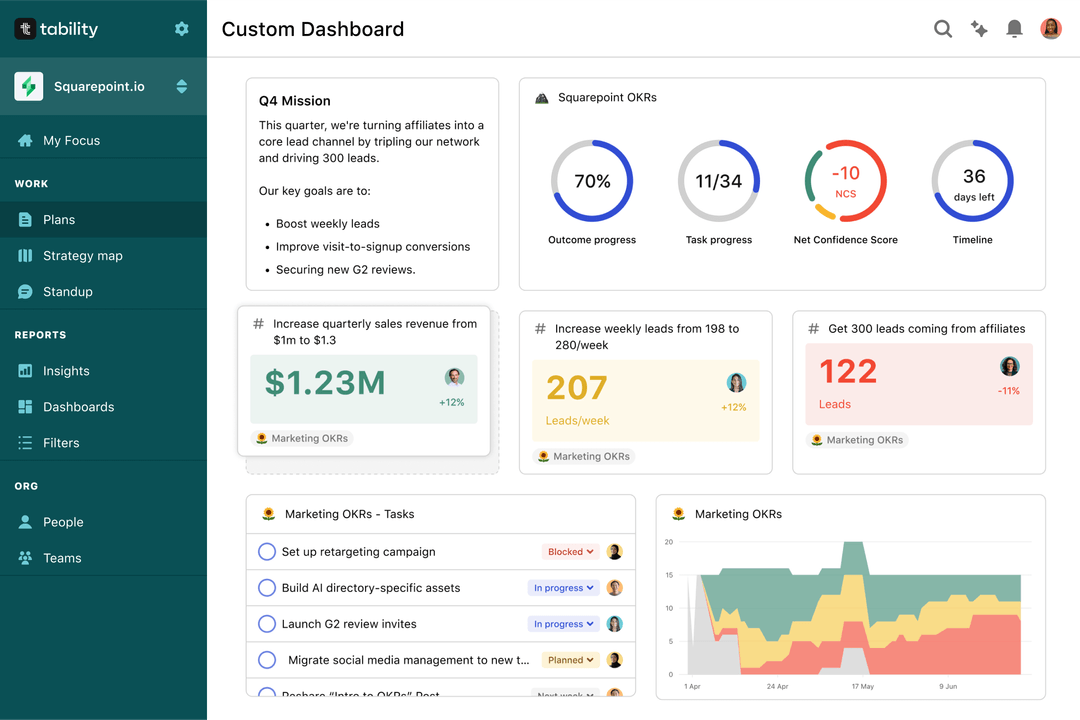
Quarterly OKRs should have weekly updates to get all the benefits from the framework. Reviewing progress periodically has several advantages:
- It brings the goals back to the top of the mind
- It will highlight poorly set OKRs
- It will surface execution risks
- It improves transparency and accountability
Most teams should start with a spreadsheet if they're using OKRs for the first time. Then, you can move to Tability to save time with automated OKR dashboards, data connectors, and actionable insights.
How to get Tability dashboards:
- 1. Create a Tability account
- 2. Use the importers to add your OKRs (works with any spreadsheet or doc)
- 3. Publish your OKR plan
That's it! Tability will instantly get access to 10+ dashboards to monitor progress, visualise trends, and identify risks early.
More System Security OKR templates
We have more templates to help you draft your team goals and OKRs.
OKRs to effectively manage turnover to enhance organizational stability
OKRs to achieve product market fit under the Sean Ellis framework
OKRs to reduce technical debt
OKRs to drive business expansion through innovative strategies
OKRs to timely resolution of IT network, hardware, software and ERP related issues
OKRs to boost the quantity of LEDs by 100