Tability is a cheatcode for goal-driven teams. Set perfect OKRs with AI, stay focused on the work that matters.
What are Security Administrator OKRs?
The Objective and Key Results (OKR) framework is a simple goal-setting methodology that was introduced at Intel by Andy Grove in the 70s. It became popular after John Doerr introduced it to Google in the 90s, and it's now used by teams of all sizes to set and track ambitious goals at scale.
Writing good OKRs can be hard, especially if it's your first time doing it. You'll need to center the focus of your plans around outcomes instead of projects.
We understand that setting OKRs can be challenging, so we have prepared a set of examples tailored for Security Administrator. Take a peek at the templates below to find inspiration and kickstart your goal-setting process.
If you want to learn more about the framework, you can read our OKR guide online.
The best tools for writing perfect Security Administrator OKRs
Here are 2 tools that can help you draft your OKRs in no time.
Tability AI: to generate OKRs based on a prompt
Tability AI allows you to describe your goals in a prompt, and generate a fully editable OKR template in seconds.
- 1. Create a Tability account
- 2. Click on the Generate goals using AI
- 3. Describe your goals in a prompt
- 4. Get your fully editable OKR template
- 5. Publish to start tracking progress and get automated OKR dashboards
Watch the video below to see it in action 👇
Tability Feedback: to improve existing OKRs
You can use Tability's AI feedback to improve your OKRs if you already have existing goals.
- 1. Create your Tability account
- 2. Add your existing OKRs (you can import them from a spreadsheet)
- 3. Click on Generate analysis
- 4. Review the suggestions and decide to accept or dismiss them
- 5. Publish to start tracking progress and get automated OKR dashboards
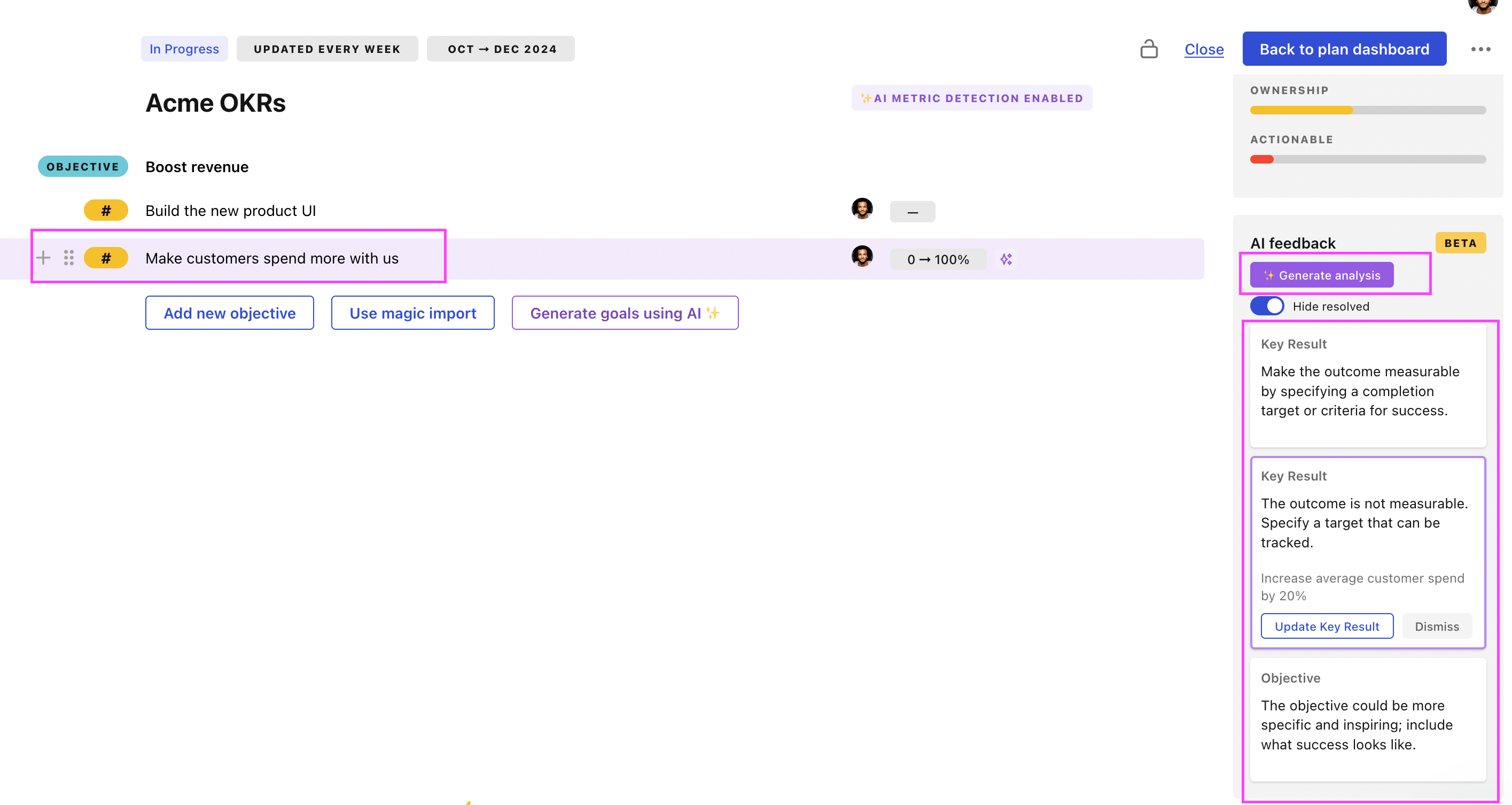
Tability will scan your OKRs and offer different suggestions to improve them. This can range from a small rewrite of a statement to make it clearer to a complete rewrite of the entire OKR.
Security Administrator OKRs examples
You will find in the next section many different Security Administrator Objectives and Key Results. We've included strategic initiatives in our templates to give you a better idea of the different between the key results (how we measure progress), and the initiatives (what we do to achieve the results).
Hope you'll find this helpful!
OKRs to upgrade and streamline physical security operations
ObjectiveUpgrade and streamline physical security operations
KRIncrease security coverage by 20% through additional surveillance systems
Investigate current surveillance system capabilities and limitations
Implement new surveillance systems accordingly
Research and identify potential additional surveillance technology
KRDecrease response times to security incidents by 25%
KRImplement a digital security management system with 100% staff training completion
Track and achieve 100% training completion
Choose a comprehensive digital security management system
Develop an all-staff training curriculum for the system
OKRs to strengthen network security through enhanced logging capabilities
ObjectiveStrengthen network security through enhanced logging capabilities
KRImplement centralized logging infrastructure to capture and store network activity data
Regularly monitor and maintain the centralized logging infrastructure to ensure uninterrupted data capture
Assess existing network infrastructure to identify suitable centralized logging solutions
Configure the centralized logging infrastructure to collect and store the network activity data
Determine the appropriate tools and technologies required for capturing network activity data
KRIncrease network security by configuring an intrusion detection system (IDS) with real-time monitoring capabilities
KRImprove incident response effectiveness by integrating logging data with a security information and event management (SIEM) system
Regularly review and fine-tune the integration and alerting processes to optimize incident response
Analyze current logging data sources and identify gaps for integration with the SIEM system
Develop standardized alerting rules within the SIEM system based on integrated logging data
Configure the SIEM system to ingest and aggregate logging data from all relevant sources
KRIdentify and resolve security vulnerabilities by regularly reviewing and analyzing network log data
Set up a regular schedule for reviewing and analyzing network log data
Generate reports based on network log data analysis to prioritize and address vulnerabilities
Implement necessary measures to resolve identified security vulnerabilities promptly and effectively
Use security software to identify and monitor potential security vulnerabilities
OKRs to fully integrate Abnormal Security tool in SecOps ecosystem with IT partnership
ObjectiveFully integrate Abnormal Security tool in SecOps ecosystem with IT partnership
KREliminate 75% of detected security threats using the Abnormal Security tool by term end
Use Abnormal Security tool to neutralize threats
Identify and analyze detected security threats
Complete training on Abnormal Security tool
KRAchieve 90% Abnormal Security tool deployment across all IT infrastructure within quarter
Identify systems not yet using the Abnormal Security tool
Develop a staggered implementation schedule for all remaining infrastructure
Monitor and report on deployment progress weekly
KRConduct 3 collaborative training sessions to foster seamless use and understanding among SecOps team
Prepare training materials and exercises
Schedule 3 collaborative training sessions
Determine training topics relevant to SecOps team
OKRs to secure local channels and gain market insights
ObjectiveSecure local channels and gain market insights
KRConduct regular market research to gather local market data and information
Conduct surveys or interviews to gather insights and preferences of local customers
Identify key competitors and their market share in the local market
Monitor industry trends and analyze data to identify emerging opportunities in the local market
KREstablish partnerships with local stakeholders to enhance channel security
Collaborate with stakeholders to develop and implement strategies for enhancing channel security
Identify key local stakeholders with expertise in channel security
Initiate meetings with stakeholders to discuss potential partnership opportunities
KRIncrease security measures on local channels to reduce unauthorized access
Implement two-factor authentication for all user accounts on local channels
Conduct regular security audits and penetration testing on local channels to identify and resolve vulnerabilities
Regularly update and patch software on local channels to address security vulnerabilities
KRImplement data analytics tools to analyze market trends and consumer behavior
Train and educate the team on how to effectively use the selected data analytics tools
Research and compare various data analytics tools available in the market
Determine key metrics and indicators to track market trends and consumer behavior
OKRs to enhance product and component Quality, Security, & Performance
ObjectiveEnhance product and component Quality, Security, & Performance
KRImprove product performance by reducing load time by 15%
Optimize graphics and frontend components to speed up rendering
Implement efficient algorithms to make the software more effective
Upgrade server resources to enhance load capacity and speed
KRIncrease test coverage of products by 20% to retain quality
Develop robust test cases for these identified areas
Identify areas of product with low or no test coverage
Implement these tests and analyze test coverage results
KRImplement a two-step verification process to enhance security by 30%
Select and purchase a suitable verification system
Research secure two-step verification options
Train staff on new verification processes
OKRs to improve Identity Access Management for large scale clients
ObjectiveImprove Identity Access Management for large scale clients
KRReduce access credential errors by 20%
Introduce regular password update reminders for employees
Implement a comprehensive access credential training program
Upgrade access security software to reduce login errors
KRImplement two-factor authentication for 90% of big customers
Deploy system to selected clients
Develop and test two-factor authentication system
Identify 90% of biggest clients requiring two-factor authentication
KRIncrease security incident response speed by 30%
Train staff in faster threat identification procedures
Implement automated threat detection and response tools
Streamline incident reporting and escalation processes
OKRs to maintain up-to-date security patches on our infrastructure
ObjectiveMaintain up-to-date security patches on our infrastructure
KRAssess and catalog current state of security patches within two weeks
Create a comprehensive catalog of findings
Identify all systems and software requiring security updates
Verify and document the existing security patches
KRImplement 100% of identified necessary security updates by quarter's end
Develop and execute a schedule for updates
Complete and verify each security update
Identify all required security updates
KRDevelop and initiate routine weekly checks to confirm security patch updates
Establish routine checks for these updates
Identify necessary security patches weekly
Implement and confirm successful patch updates
OKRs to enhance the organization's cybersecurity infrastructure
ObjectiveEnhance the organization's cybersecurity infrastructure
KRImplement multi-factor authentication for all internal systems by the end of Q2
Implement selected multi-factor authentication solution
Assess current authentication methods across all systems
Identify suitable multi-factor authentication solutions
KRConduct cybersecurity training programs for 90% of employees
Identify the key cybersecurity principles for training content
Organize training schedules for employees
Evaluate post-training comprehension and application
KRCarry out system vulnerability assessment every week to spot and fix any gaps
Implement necessary fixes to detected vulnerabilities immediately
Analyze assessment results to identify security gaps
Schedule weekly system vulnerability assessments
OKRs to implement effective vulnerability management processes
ObjectiveStrengthen our vulnerability management procedures
KRReduce high-priority vulnerabilities by 30% through consistent scanning and patching
KRTrain all employees on vulnerability management best practices and create an awareness program
KRImplement a continuous vulnerability scanning process for all systems and applications
KRDevelop and implement a comprehensive vulnerability management policy based on industry standards
Security Administrator OKR best practices
Generally speaking, your objectives should be ambitious yet achievable, and your key results should be measurable and time-bound (using the SMART framework can be helpful). It is also recommended to list strategic initiatives under your key results, as it'll help you avoid the common mistake of listing projects in your KRs.
Here are a couple of best practices extracted from our OKR implementation guide 👇
Tip #1: Limit the number of key results
The #1 role of OKRs is to help you and your team focus on what really matters. Business-as-usual activities will still be happening, but you do not need to track your entire roadmap in the OKRs.
We recommend having 3-4 objectives, and 3-4 key results per objective. A platform like Tability can run audits on your data to help you identify the plans that have too many goals.
Tip #2: Commit to weekly OKR check-ins
Don't fall into the set-and-forget trap. It is important to adopt a weekly check-in process to get the full value of your OKRs and make your strategy agile – otherwise this is nothing more than a reporting exercise.
Being able to see trends for your key results will also keep yourself honest.
Tip #3: No more than 2 yellow statuses in a row
Yes, this is another tip for goal-tracking instead of goal-setting (but you'll get plenty of OKR examples above). But, once you have your goals defined, it will be your ability to keep the right sense of urgency that will make the difference.
As a rule of thumb, it's best to avoid having more than 2 yellow/at risk statuses in a row.
Make a call on the 3rd update. You should be either back on track, or off track. This sounds harsh but it's the best way to signal risks early enough to fix things.
Save hours with automated Security Administrator OKR dashboards
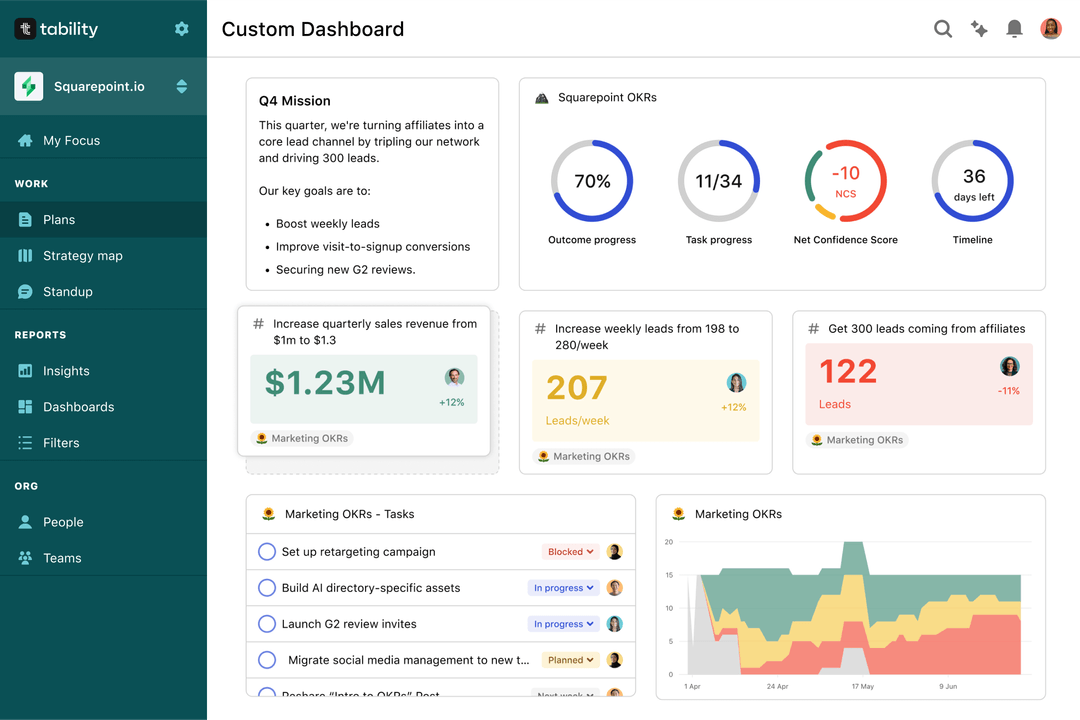
Your quarterly OKRs should be tracked weekly if you want to get all the benefits of the OKRs framework. Reviewing progress periodically has several advantages:
- It brings the goals back to the top of the mind
- It will highlight poorly set OKRs
- It will surface execution risks
- It improves transparency and accountability
Most teams should start with a spreadsheet if they're using OKRs for the first time. Then, you can move to Tability to save time with automated OKR dashboards, data connectors, and actionable insights.
How to get Tability dashboards:
- 1. Create a Tability account
- 2. Use the importers to add your OKRs (works with any spreadsheet or doc)
- 3. Publish your OKR plan
That's it! Tability will instantly get access to 10+ dashboards to monitor progress, visualise trends, and identify risks early.
More Security Administrator OKR templates
We have more templates to help you draft your team goals and OKRs.
OKRs to successfully launch an online POD store on Shopify using Printify
OKRs to improve website's overall usability
OKRs to launch a successful new insurance product
OKRs to secure venture capital funding for Plika's Latam expansion
OKRs to strengthen HR compliance and DEI program adherence in Kenya
OKRs to promote an environment fostering teamwork, learning, and growth